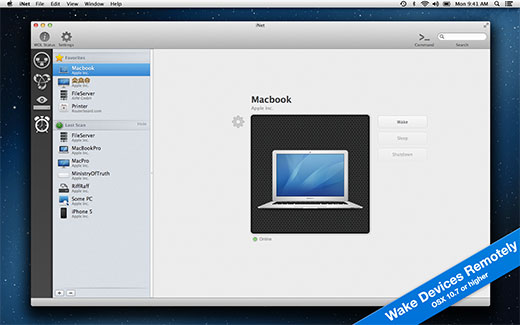
INet Network Scanner 2.7 For MacOS. INet Network Scanner iNet – explore your network! Find out about security risks and keep your network under control. With iNet you know exactly what's going on! This easy to use App outlines a computer network even to the unexperienced user. RFC 6020 YANG October 2010 1.Introduction YANG is a data modeling language used to model configuration and state data manipulated by the Network Configuration Protocol (NETCONF), NETCONF remote procedure calls, and NETCONF notifications. INet Network Scanner for Macintosh - Get a profound overview about your computer network with this easy to understand toolbox. Not only for IT professionals.
2) A Raspberry Pi power adapter or a 2.1A USB power bank 3) A SD card reader for flashing Raspbian OS onto the microSD card. 4) A microSD card 5) A network switch 6) Ethernet cables 7) A Wi-Fi network to connect the Raspberry Pi to 8) A computer/laptop for configuring the Raspberry Pi.
Find out about security risks and keep your network under control. This easy to use App outlines a computer network even to the unexperienced user. Is somebody using your network without your knowledge? Which devices are currently online? Which access ports are open?
macOS 10.8 or later 64-bit
DOWNLOAD
uploadgig
https://uploadgig.com/file/download/5535c99449E41Acd/coMQ15hG_iNet_Network_Scanner_2.7.7_MAS_TNT_.rar
rapidgator
https://rapidgator.net/file/d1dd5a3f102e975fdaf12844c227b6f6/coMQ15hG_iNet_Network_Scanner_2.7.7_MAS_TNT_.rar.html
nitroflare
http://nitroflare.com/view/ACC4DEFA6E186E4/coMQ15hG_iNet_Network_Scanner_2.7.7_MAS_TNT_.rar
Report Dead Link(s)
Only Registed user can add comment, view hidden links and more, please register now
Name
arp-scan - The ARP scannerSynopsis
arp-scan [options] [hosts..]Target hosts must be specified on the command line unless the --file option is given, in which case the targets are read from the specified fileinstead, or the --localnet option is used, in which case the targets are generated from the network interface IP address and netmask.
You will need to be root, or arp-scan must be SUID root, in order to run arp-scan, because the functions that it uses to read and writepackets require root privilege.
The target hosts can be specified as IP addresses or hostnames. You can also specify the target as IPnetwork/bits (e.g. 192.168.1.0/24) to specifyall hosts in the given network (network and broadcast addresses included), IPstart-IPend (e.g. 192.168.1.3-192.168.1.27) to specify all hosts in theinclusive range, or IPnetwork:NetMask (e.g. 192.168.1.0:255.255.255.0) to specify all hosts in the given network and mask.
Description
arp-scan sends ARP packets to hosts on the local network and displays any responses thatare received. The network interface to use can be specified with the --interface option. If this option is not present, arp-scan will search thesystem interface list for the lowest numbered, configured up interface (excluding loopback). By default, the ARP packets are sent to the Ethernet broadcastaddress, ff:ff:ff:ff:ff:ff, but that can be changed with the --destaddr option.The target hosts to scan may be specified in one of three ways: by specifying the targets on the command line; by specifying a file containing the targetswith the --file option; or by specifying the --localnet option which causes all possible hosts on the network attached to the interface (asdefined by the interface address and mask) to be scanned. For hosts specified on the command line, or with the --file For hosts specified on the command line,or with the --file option, you can use either IP addresses or hostnames. You can also use network specifications IPnetwork/bits,IPstart-IPend, or IPnetwork:NetMask.
The list of target hosts is stored in memory. Each host in this list uses 28 bytes of memory, so scanning a Class-B network (65,536 hosts) requires about1.75MB of memory for the list, and scanning a Class-A (16,777,216 hosts) requires about 448MB.
arp-scan supports Ethernet and 802.11 wireless networks. It could also support token ring and FDDI, but they have not been tested. It does notsupport serial links such as PPP or SLIP, because ARP is not supported on them.
The ARP protocol is a layer-2 (datalink layer) protocol that is used to determine a host's layer-2 address given its layer-3 (network layer) address. ARPwas designed to work with any layer-2 and layer-3 address format, but the most common use is to map IP addresses to Ethernet hardware addresses, and this iswhat arp-scan supports. ARP only operates on the local network, and cannot be routed. Although the ARP protocol makes use of IP addresses, it is not anIP-based protocol and arp-scan can be used on an interface that is not configured for IP.
ARP is only used by IPv4 hosts. IPv6 uses NDP (neighbour discovery protocol) instead, which is a different protocol and is not supported by arp-scan.
One ARP packet is sent for each for each target host, with the target protocol address (the ar$tpa field) set to the IP address of this host. If a host doesnot respond, then the ARP packet will be re-sent once more. The maximum number of retries can be changed with the --retry option. Reducing the number ofretries will reduce the scanning time at the possible risk of missing some results due to packet loss.
You can specify the bandwidth that arp-scan will use for the outgoing ARP packets with the --bandwidth option. By default, it uses a bandwidthof 256000 bits per second. Popchar x 7 2 download free. Increasing the bandwidth will reduce the scanning time, but setting the bandwidth too high may result in an ARP storm which candisrupt network operation. Also, setting the bandwidth too high can send packets faster than the network interface can transmit them, which will eventuallyfill the kernel's transmit buffer resulting in the error message: No buffer space available. Another way to specify the outgoing ARP packet rate is withthe --interval option, which is an alternative way to modify the same underlying parameter.
The time taken to perform a single-pass scan (i.e. with --retry=1) is given by:Where n is the number of hosts in the list, i is the time interval between packets (specified with --interval, or calculated from--bandwidth), t is the timeout value (specified with --timeout) and o is the overhead time taken to load the targets into the listand read the MAC/Vendor mapping files. For small lists of hosts, the timeout value will dominate, but for large lists the packet interval is the most importantvalue.
With 65,536 hosts, the default bandwidth of 256,000 bits/second (which results in a packet interval of 2ms), the default timeout of 100ms, and a single pass( --retry=1), and assuming an overhead of 1 second, the scan would take 65536*0.002 + 0.1 + 1 = 132.172 seconds, or about 2 minutes 12 seconds. Deck set 2 0 13 equals.
Any part of the outgoing ARP packet may be modified through the use of the various --arpXXX options. The use of some of these options may make theoutgoing ARP packet non RFC compliant. Different operating systems handle the various non standard ARP packets in different ways, and this may be used tofingerprint these systems. See arp-fingerprint(1) for information about a script which uses these options to fingerprint the target operatingsystem.
The table below summarises the options that change the outgoing ARP packet. In this table, the Field column gives the ARP packet field name from RFC826, Bits specifies the number of bits in the field, Option shows the arp-scan option to modify this field, and Notes gives thedefault value and any other notes.| Outgoing ARP Packet Options |
| Field Bits Option Notes |
| ar$hrd 16 --arphrd Default is 1 (ARPHRD_ETHER) |
| ar$pro 16 --arppro Default is 0x0800 |
| ar$hln 8 --arphln Default is 6 (ETH_ALEN) |
| ar$pln 8 --arppln Default is 4 (IPv4) |
| ar$op 16 --arpop Default is 1 (ARPOP_REQUEST) |
| ar$sha 48 --arpsha Default is interface h/w address |
| ar$spa 32 --arpspa Default is interface IP address |
| ar$tha 48 --arptha Default is zero (00:00:00:00:00:00) |
| ar$tpa 32 None Set to the target host IP address |
The most commonly used outgoing ARP packet option is --arpspa, which sets the source IP address in the ARP packet. This option allows the outgoingARP packet to use a different source IP address from the outgoing interface address. With this option it is possible to use arp-scan on an interfacewith no IP address configured, which can be useful if you want to ensure that the testing host does not interact with the network being tested.
It is also possible to change the values in the Ethernet frame header that proceeds the ARP packet in the outgoing packets. The table below summarises theoptions that change values in the Ethernet frame header.| Outgoing Ethernet Frame Options |
| Field Bits Option Notes |
| Dest Address 48 --destaddr Default is ff:ff:ff:ff:ff:ff |
| Source Address 48 --srcaddr Default is interface address |
| Protocol Type 16 --prototype Default is 0x0806 |
The most commonly used outgoing Ethernet frame option is --destaddr, which sets the destination Ethernet address for the ARP packet.--prototype is not often used, because it will cause the packet to be interpreted as a different Ethernet protocol.
Any ARP responses that are received are displayed in the following format:Nxpowerlite 8 0 8 0. Where IP Address is the IP address of the responding target, Hardware Address is its Ethernet hardware address (also known as the MAC address)and Vendor Details are the vendor details, decoded from the hardware address. The output fields are separated by a single tab character.
The responses are displayed in the order that they are received, which is not always the same order as the requests were sent because some hosts may respondfaster than others.
The vendor decoding uses the files ieee-oui.txt, ieee-iab.txt and mac-vendor.txt which are supplied with arp-scan. Theieee-oui.txt and ieee-iab.txt files are generated from the OUI and IAB data on the IEEE website athttp://standards.ieee.org/regauth/oui/ieee-oui.txt and http://standards.ieee.org/regauth/oui/iab.txt. The Perl scripts get-oui andget-iab, which are included in the arp-scan package, can be used to update these files with the latest data from the IEEE website. Themac-vendor.txt file contains other MAC to Vendor mappings that are not covered by the IEEE OUI and IAB files.
Almost all hosts that support IP will respond to arp-scan if they receive an ARP packet with the target protocol address (ar$tpa) set to their IPaddress. This includes firewalls and other hosts with IP filtering that drop all IP traffic from the testing system. For this reason, arp-scan is auseful tool to quickly determine all the active IP hosts on a given Ethernet network segment.
Options
or -y
, default=0x0806. This sets the 16-bit protocol type field in the Ethernet frame header. Setting this to anon-default value will result in the packet being ignored by the target, or send to the wrong protocol stack. This option is probably not useful, and is onlypresent for completeness.
or -A
. This data is appended to the end of the ARP packet, after the data. Most,if not all, operating systems will ignore any Padding. The default is no padding, although the Ethernet driver on the sending system may pad the packet to theminimum Ethernet frame length.
or -W
. This option causes received ARP responses to be written to a pcap savefile with the specified name. Thissavefile can be analyzed with programs that understand the pcap file format, such as 'tcpdump' and 'wireshark'.

